JP Morgan Chase needs to completely revamp its current cyber security defense infrastructure. The security infrastructure products in place aren’t cutting it as a primary defense system. They should be used as a third line of defense. A big problem with today’s product is they work in silos that don’t talk to each other. Another problem is these security companies have thousands of customers to support, being all things to all customers. That isn’t going to work. The financial institutions need their own dedicated security infrastructure that is built from the ground up, specifically tailored to meet their requirements.
The next problem is the Defense-in-depth strategy. The current strategy is inadequate to protect banks, and needs some serious updating. Defense-in-depth is a strategy for achieving information assurance that is based on the “Protect, Detect, and React paradigm”. The three pillars that help achieve information assurance are People, Technology, and Operations. The People Pillar is the weak link of the strategy. Security cannot depend on people making the right choices and following security policies day-in day-out. JP Morgan has 245,000 employees. No way every single employee is going to play by the rules. Someone somewhere is going to blow it and open the wrong email. And the overworked overstretched SecOp teams are too few in number to catch every alert. Humans are error-prone, and we make mistakes every day. The People Pillar of the Defense-in-depth strategy will always be the weak link that makes attacks easier.
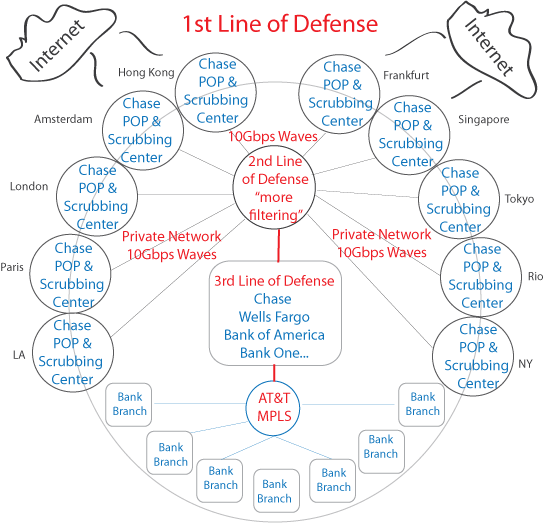
The Solution: JP Morgan Chase should take $50M out of the $250M cyber security budget and build its own global cyber security defense system from scratch. Other banks like Wells Fargo, Bank of America, and so on, can participate and create a banking alliance focused on global cyber security. Its time the financial institutions take the lead and not depend too heavily on the security industry. At the core of the security defense system is a private network running on redundant 10Gb waves that interconnect POPs. Only bank traffic will be allowed on the network. There will be no mixing and matching of http/ https traffic with non-banking clients. The 2nd line of defense is another Super POP that does additional filtering. Here is an illustration.
JP Morgan Chase CDN Security Shield