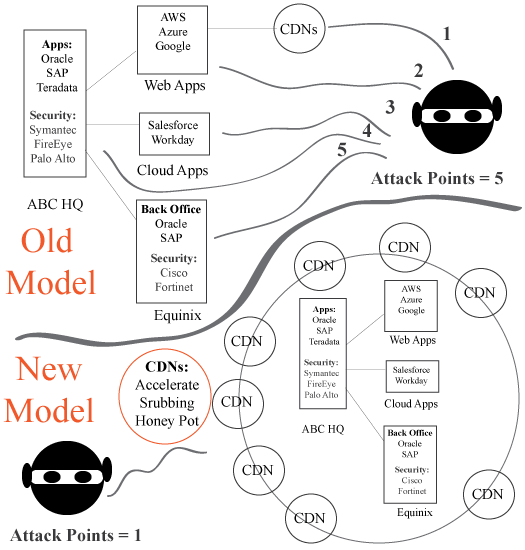
The current security business model needs radical transformation. The force needed to disrupt the security industry is only likely to come from an external group. Sure, the security industry is innovating at the fastest pace ever, but when compared to the success of threat actors, the security model has fallen short. Its too constrained, lacking in innovation and creativity, and operating within a silo. What the security industry needs is a “pre-cloud Amazon AWS” that can dismantle the status quo, and bring order from the chaos. Amazon single handily wreaked havoc on the $100B+ compute, storage and networking markets. Thus, someone or some group can do the same to the security industry. The question is can the innovation driven CyberSecurity CDNs take the driver’s seat, force the change, dismantle the current security business model, and rip away billions from the likes of Cisco, FireEye, Palo Alto, F5, Barracuda Networks, and others.
The CyberSecurity CDN start-up must take the first step of action, invest the resources, and bet the house on this new strategy. For starters, CDNs can invest in a global honeypot network that is able to track every type of malware, from every part of the globe, all the way to the last mile. Then expand into phising solutions, mobility security, cloud SEIM, and so on. CDNs can no longer afford to be a spectator, letting the traditional security vendor try to figure things out. CDNs must invade the territory of the traditional security vendor, such as Symantec, Palo Alto, FireEye, Cisco, and F5, and create competing products, built for CDN infrastructure. CDN infrastructure equals unlimited scalability, instantaneous configurability, and global last mile security solutions. Yes, it might cost a million or two, to start a simple security project of this type, but the payoff can be legendary.
New CDN Hacker Business Model Features
- Accelerate: DSA, FEO, Mobile, RAN, TCP/IP Optimizations…
- Standard Security: DDoS Mitigation, WAF, Bot Detection…
- Advanced Security: Sand boxing, Malware Detection/Removal, ATP, Phising Solutions, Mobile Security…