Traceable AI was founded in 2018 by Jyoti Bansal and Sanjay Nagaraj; the startup raised $60M in Series B and $79M in total, valuing them at $450M in May 2022. The most impressive part of all this is the founder, Jyoti.
Jyoti founded AppDynamics, which sold to Cisco for $3.7B. In the same year, he founded Harness, which has raised $425M. The valuation for Harness is $3.7B; thus, Jyoti is the CEO of two successful startups.
Traceable AI
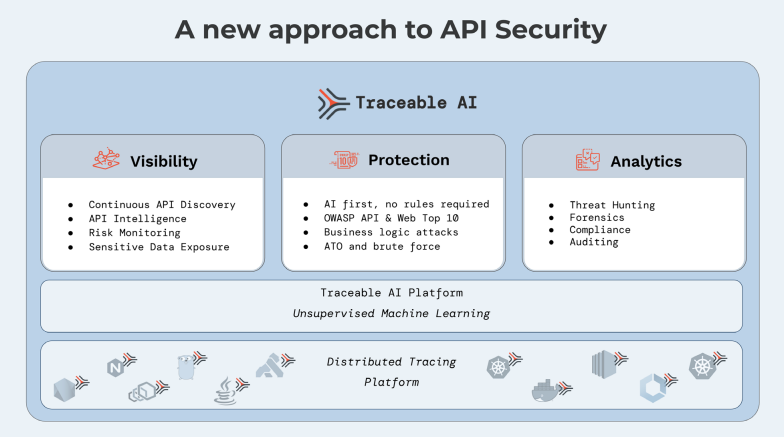
Traceable AI provides API security. The platform leverages machine learning, big data, and data lake technologies to detect anomalies in API traffic. Just like the other API security platforms we’ve covered, the startup provides the basic features of API discovery, detection of vulnerabilities and misconfiguration, and the ability to monitor attackers and their activity.
Background
- Company: Traceable AI
- Founded: 2018
- HQ: San Francisco
- Raised: $80M
- # of Employees: 106
- Founders: Jyoti Bansal (CEO) and Sanjay Nagaraj (CTO)
- Product: API Security
- Customers:
Observability
The Traceable platform leverages an application observability platform. The core technology of the platform is a data lake. As data flows through the application, user-driven transactions are collected and analyzed. Afterward, the machine learning engine creates a baseline of activity that maps the “business logic into a logistical model.” As user activity changes, the ML models change with it to track normal traffic behavior.
Machine Learning
The Traceable platform excels in working in a microservices-based environment. In a Kubernetes setup, agents are installed on a sidecar container. The goal is to collect data such as user access patterns and intent, which is used to develop accurate statistical application usage models.
Traceable works with internal and external instrumentation. For internal instrumentation, AI agents are deployed inside the applications. For external instrumentation, user traffic is mirrored and copied to the platform for analysis. Together, they are used to provide complete API security at runtime.
Features
- Discovery of all APIs, including shadow and orphaned
- Detects vulnerabilities in real-time, especially those caused by misconfigurations
- Security posture insight in the microservices-based application
- Detects and blocks logic bombs and business logic abuse
- Maps topologies and data flows between connecting edge APIs
- Risk scores based on attack likelihood
- Observe threat actors and their activity across apps
- Rate limiting and IP range block available
- Protects against brute force attacks
- Integrates into API gateways

